Device Identity for high-consequence autonomous & industrial environments
CMMC Level 2 requires cryptographic identity for every system accessing CUI. Smallstep enforces hardware-bound device identity—eliminating copyable credentials and enabling certificate-based access across devices, workloads, and automation.

Defense and dual use
Designed for organizations operating autonomous, safety-critical, or cyber-physical systems—where credential theft can have operational and real-world consequences, and enforcement must function in distributed and disconnected environments. Protect mission networks, SaaS and internal applications, engineering environments, and edge/autonomous systems with certificate-based access that continues to work through intermittent connectivity.
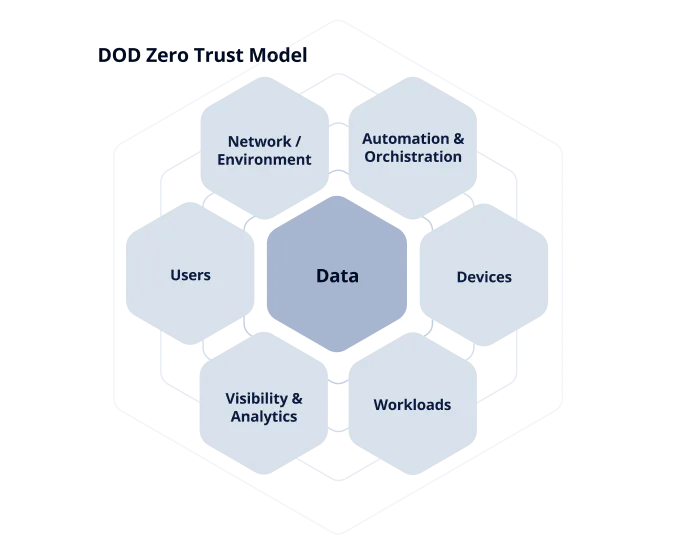
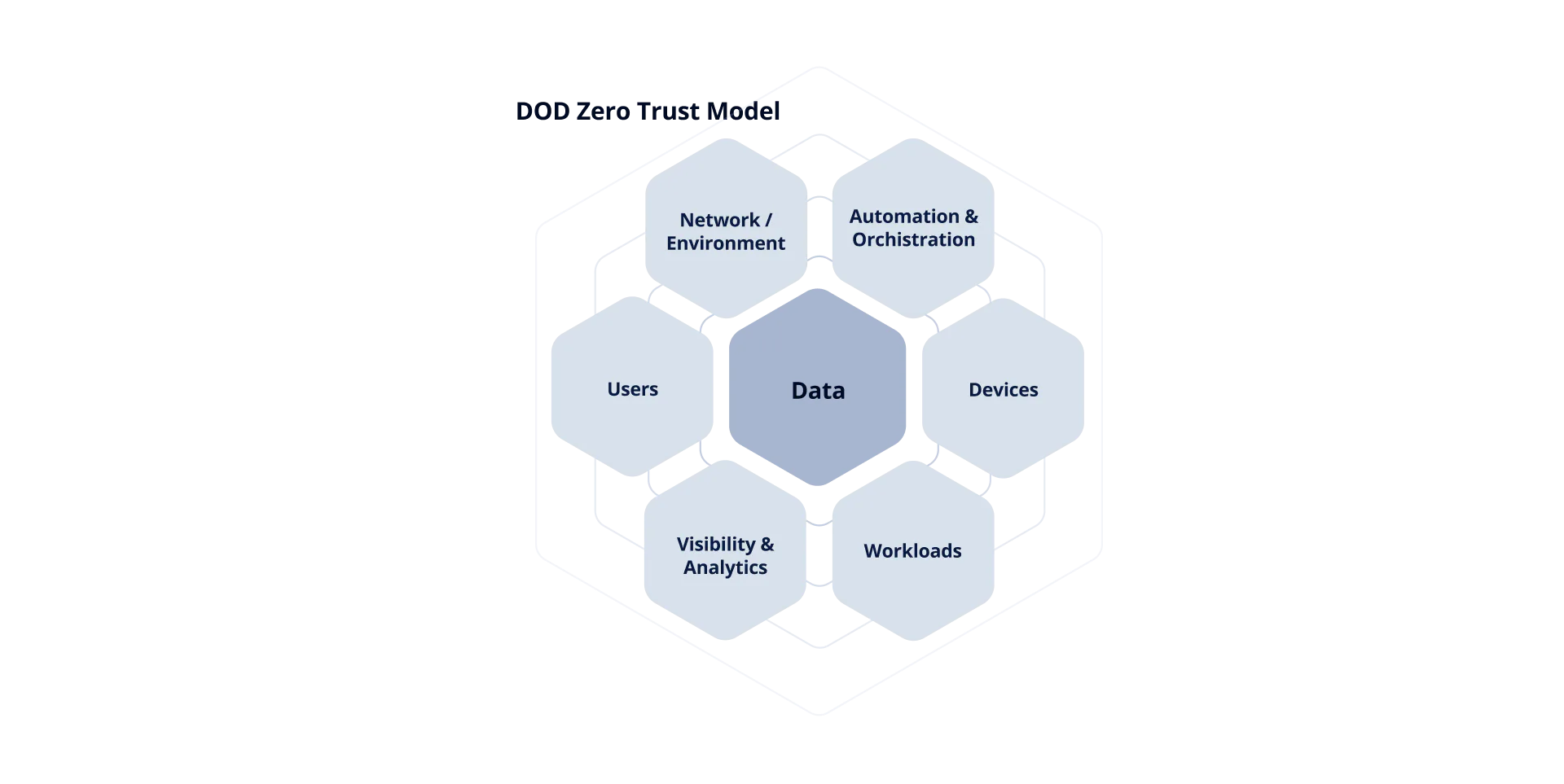
Zero Trust fails without device identity
CMMC Level 2 requires cryptographic identity for every system accessing CUI—users, devices, and automation included.
Trust extends past the perimeter
Fielded endpoints and distributed runtimes need provable identity when connectivity and oversight are inconsistent.
Copyable credentials break policy
If tokens and keys can be replayed, enforcement becomes a suggestion instead of a control boundary.
Autonomy amplifies drift
Agents and tools chain actions quickly. Identity and attestation become the gating layer for access and execution.
Denial of service isn’t always volumetric
In industrial environments, outages often stem from identity failures. Unmanaged devices and replayed credentials can exhaust access gateways and halt operations.
No provenance
Traditional flows don’t prove which device initiated a request—only that a credential was presented.
Revocation gap
Offboarding a device in MDM doesn’t necessarily revoke all usable credentials already copied elsewhere.

High-Consequence System Use Cases
Enforce “only known hardware can act” for humans, machines, and agents—reducing credential replay, lateral movement, and unmanaged device risk across mission and engineering environments.

Standards alignment
NIST SP 800-207 (Zero Trust): Enforces “never trust, always verify” at the device boundary using hardware-backed identity and short-lived credentials.
NIST SP 800-63: Strengthens authenticator posture by reducing reliance on reusable shared secrets (passwords/long-lived tokens) in device access paths.
CMMC / NIST SP 800-171: Helps meet access control + identification/authentication expectations by binding access to managed, validated devices and making credential lifecycle auditable.
Smallstep provides enforcement primitives, not compliance certification.

Device Identity Platform
Standardized, high-assurance enrollment and certificate lifecycle management across macOS, Windows, Linux, Android, and ChromeOS—built for brownfield fleets and mission-scale rollouts.

MCP AI Security
AI agents and MCP toolchains introduce non-human automation that can take real actions—often using copied credentials outside traditional network and identity boundaries.
Smallstep provides cryptographic runtime identity and access enforcement, replacing API keys with short-lived, hardware-backed certificates that prove where a request originates and what it’s allowed to access.
When you also need cryptographic identification of the agent itself, Smallstep integrates with partners like Keycard to extend identity from runtime to actor.

Industrial & Manufacturing Sites
Designed for OT/edge environments where availability is paramount and identity failures can halt operations.
- Rogue devices attempting to enroll and hammer gateways
- Replayed credentials causing repeated auth loops, lockouts, and throttling
- Unmanaged endpoints rejoining during incident recovery windows
- Shared credentials crossing zones despite segmentation policies
AI toolchains need enforceable provenance
| Capability | API Key | Certificates |
|---|---|---|
| Rotation & lifecycle | Long-lived | Short-lived |
| Credential portability | Keys/secrets can be copied | Non-exportable hardware-bound keys |
| Provenance | None | Cryptographically verifiable |
| Enforcement | Depends on app-specific signals | Certificates work almost everywhere (Wi‑Fi / VPN / ZTNA / SSO) |
| Phishing resistance | Stolen credential still authenticate | Credential tied to the device’s secure element |
Scroll to the right to see more →
Common Starting Points
Wi-Fi / 802.1X
Require hardware-bound client certificates at RADIUS to eliminate shared secrets and rogue device access.
SSO device trust
Use device identity as a factor at login to enforce policy per session.
Build & repo access
Lock access to Git and build systems to verified devices and short-lived credentials.

Integrates with your existing stack
The platform integrates with existing identity providers, infrastructure, and security tooling, including AI runtimes and MCP-based systems. It extends cryptographic identity and policy enforcement to agents, tools, and automated workflows without requiring architectural replacement. This allows trust controls to remain consistent as execution shifts from users and services to autonomous systems.
The foundation for secure device access
Secure mission networks, engineering systems, and AI toolchains with hardware-backed device identity.