Device Identity for Enterprise IT
Smallstep secures corporate devices, networking, and source code with hardware-backed device identity. The same policies enforce trusted access to SaaS, internal apps, AI tools, and MCP-enabled services.


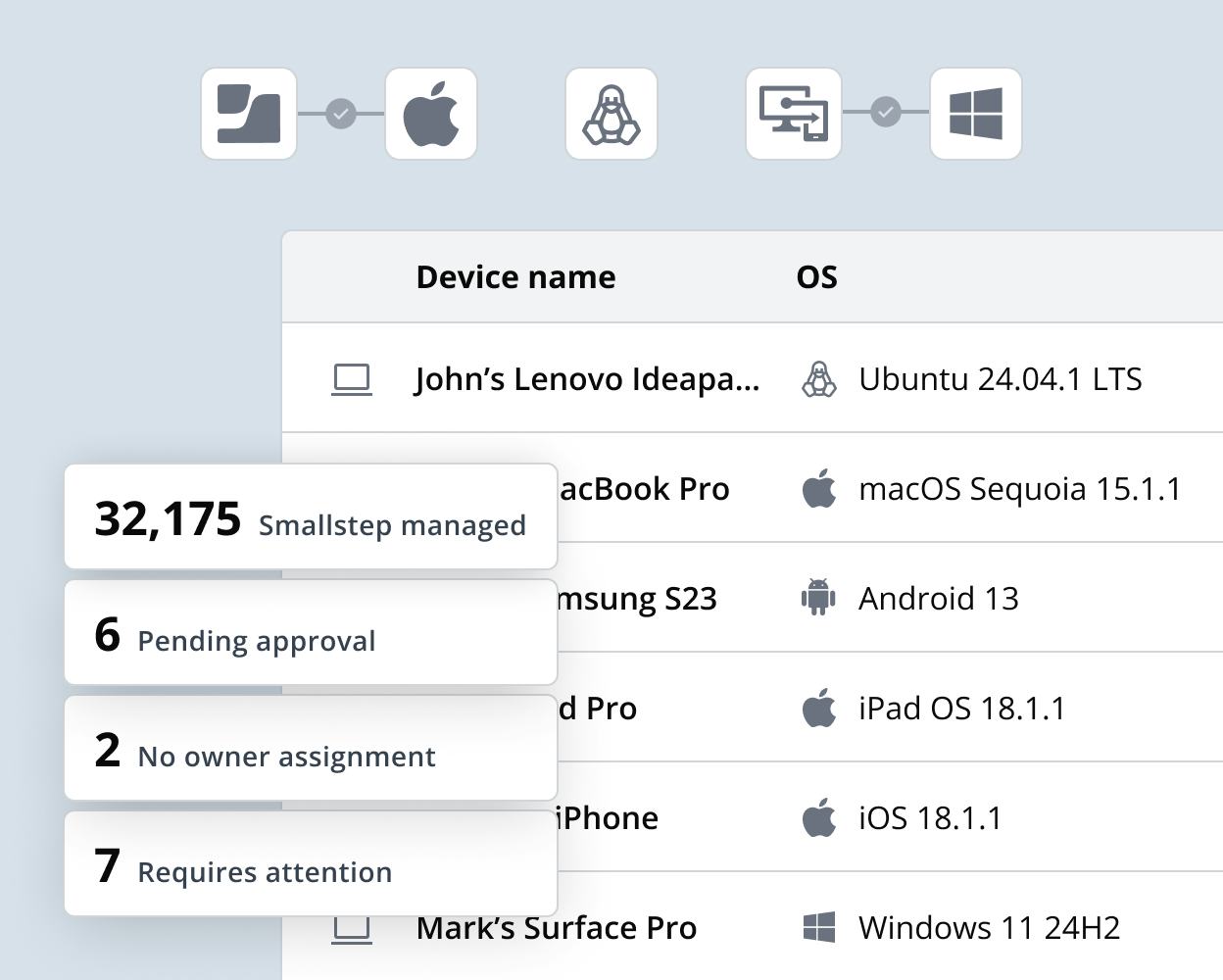
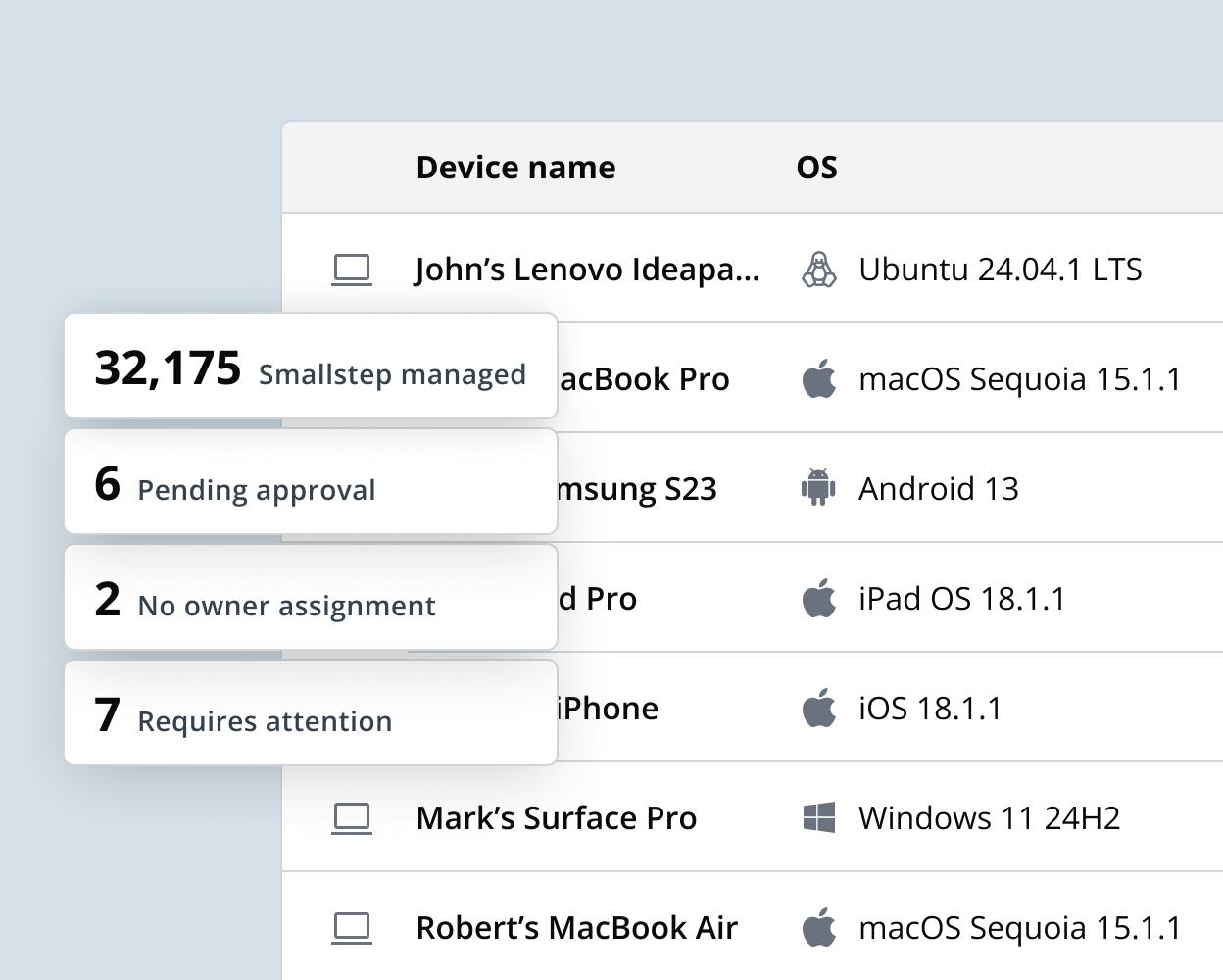
Feel better about your device inventory
Do you really know where your devices are? Without a complete and verified list of all your trusted company devices, you can’t confidently implement device identity as an authentication factor. Smallstep's Device Inventory is a cybersecurity tool, not an ITAM replacement.
Shine light on blind spots
Even the most robust user authentication (SSO, MFA, background checks) can’t detect which actual machine is being used. If employees—or attackers with stolen user credentials—can log in from unverified laptops, personal gaming rigs, or ephemeral virtual machines, your Zero Trust efforts lose much of their value. That’s where Device Identity comes in: it ensures only legitimate, recognized corporate devices can initiate connections to your most sensitive resources.
Hardware-backed device credentials
Device Identity ensures that only company-owned devices can access your enterprise's most sensitive resources, including Wi-Fi networks, VPNs, financial dashboards, intellectual property, and databases with GDPR-scoped PII. Smallstep device identity provides the strongest possible guarantee of authentic device identity, preventing credential exfiltration, phishing, and impersonation attacks.
Learn about the “Other Half” of identity
You could be missing half of Zero Trust. You have figured out user identity, but what about devices?
Download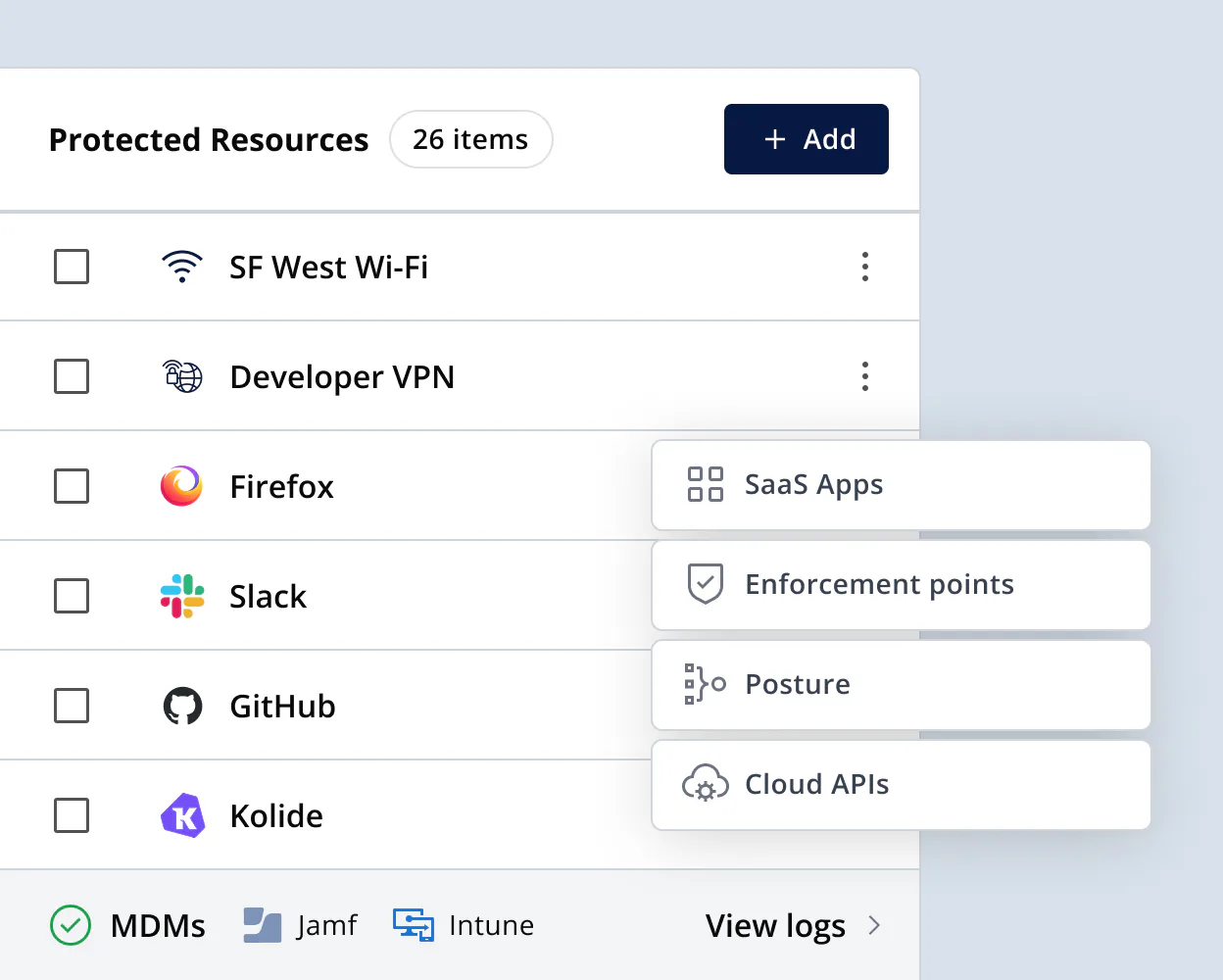
Learn more about the platform
The Smallstep platform helps mitigate numerous cybersecurity threats – from phishing to advanced hardware attacks – without impacting end-user workflows.
Enforce device identity everywhere
Whether you’re working towards a compliance standard, closing gaps in policy enforcement, or preventing nation-state attacks, our team is here to show you how the Smallstep Platform can help.